Q495
(none)
Which function is performed by DHCP snooping?
Correct Answer:
D
Q496
(none)
Which plane is centralized by an SON controller?
Correct Answer:
B
Q497
(none)
Which access layer threat-mitigation technique provides security based on identity?
Correct Answer:
C
Q498
(none)
What are two similarities between UTP Cat 5e and Cat 6a cabling? (Choose two.)
Choose 2 — select all that apply
Correct Answer:
CD
Q499
(none)
Refer to the exhibit. What is the metric of the route to the 192.168.10.33/28 subnet?
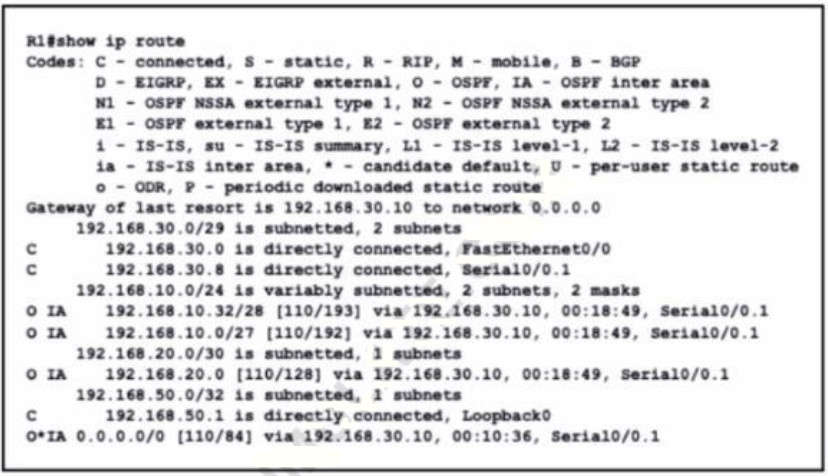
Correct Answer:
E
Q500
(none)
What are two characteristics of the distribution layer in a three-tier network architecture? (Choose two.)
Choose 2 — select all that apply
Correct Answer:
AB
The distribution layer aggregates the data received from the access layer switches before it is transmitted to the core layer for routing to its final destination. In Figure 1-6, the distribution layer is the boundary between the Layer 2 domains and the Layer 3 routed network. https://www.ciscopress.com/articles/article.asp?p=2202410&seqNum=4
Q501
(none)
What prevents a workstation from receiving a DHCP address?
Correct Answer:
B
Q502
(none)
What Is a syslog facility?
Correct Answer:
D
Q503
(none)
Which communication interaction takes place when a southbound API Is used?
Correct Answer:
B
Q504
(none)
Which port type supports the spanning-tree portfast command without additional configuration?
Correct Answer:
A